By Connor Gadbois and Marcia Gadbois

Industrial cybersecurity has entered a more exposed, strategic phase, shaped by the hard lessons manufacturing organizations learned throughout 2025. A recent article from Manufacturing Business Technology, titled “Number of ICS/OT Cyber Incidents Raises Alarms” (November 20, 2025), highlights just how serious the situation has become.
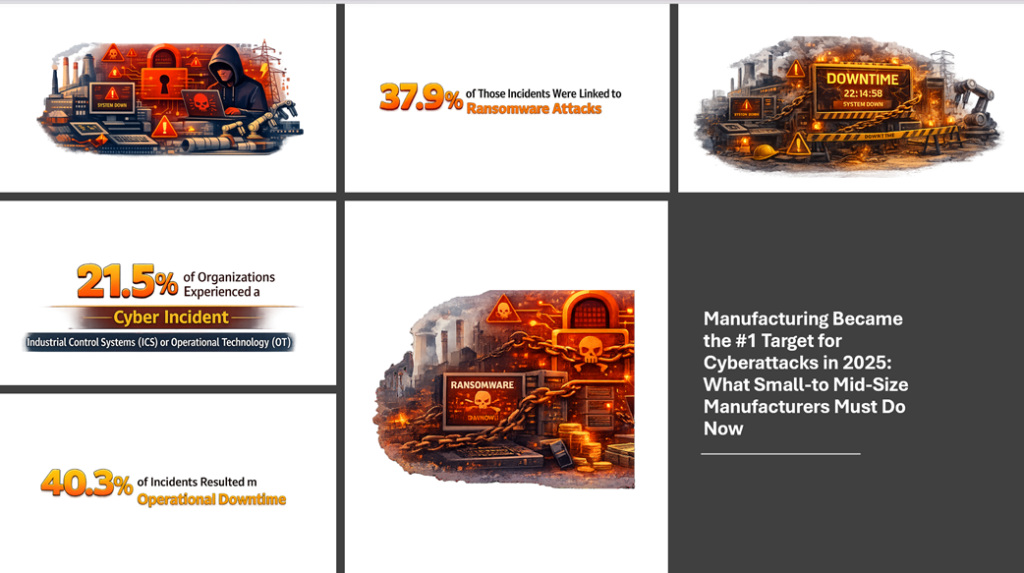
According to the report:
– 21.5% of organizations experienced a cyber incident that impacted their Industrial Control Systems (ICS) or Operational Technology (OT).
– 37.9% of those incidents were linked to ransomware attacks, demonstrating how aggressively attackers are targeting industrial environments.
– 40.3% of incidents resulted in operational downtime, directly affecting production and business continuity.
These numbers reinforce a growing reality: cybersecurity is no longer just an IT concern. For manufacturers, it has become a critical operational issue that directly impacts safety, uptime, and profitability.
Manufacturing Has Become the Primary Target
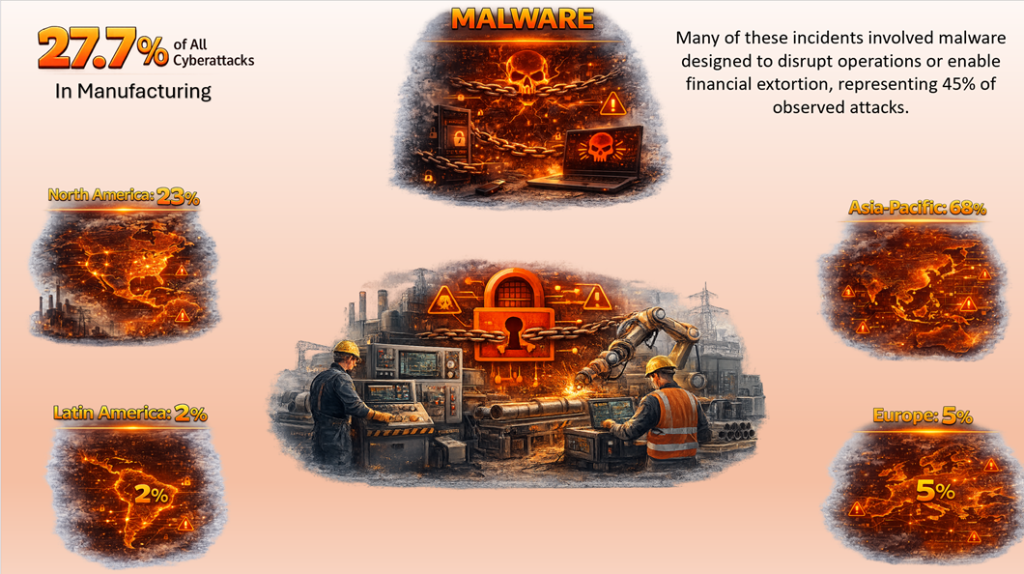
The scale of the threat becomes even clearer when looking at broader industry data. According to the latest IBM X-Force report, the manufacturing sector accounted for 27.7% of all cyberattacks in 2025, the highest share among all industries analyzed.
The report also highlights the global nature of these attacks:
– Asia-Pacific: 68% of manufacturing-related attacks
– North America: 23%
– Europe: 5%
– Latin America: 2%
Many of these incidents involved malware designed to disrupt operations or enable financial extortion, representing 45% of observed attacks. Cybercriminals increasingly recognize that operational disruption in manufacturing environments can quickly translate into financial leverage.

Why Small-to-Mid-Market Manufacturers Are Increasingly at Risk
For small-to-mid-market manufacturers, the challenge is becoming even more significant. Cyber attackers are no longer focusing only on large enterprises with deep pockets. Increasingly, they are using automation and artificial intelligence to target small-to-midsize businesses (SMBs) at scale.
Recent security research from the Data Breach Observatory confirms this shift. Their findings show that four out of five small businesses have experienced a recent data breach, highlighting how frequently SMBs are now being targeted. In fact, SMBs were the primary target of hackers in 2025, accounting for 70.5% of the data breaches identified in the report. Companies with between 1 and 249 employees were the most vulnerable to cybersecurity incidents throughout the year.
While industries such as retail and media/entertainment experienced the highest number of attacks, SMB manufacturers are also increasingly exposed, particularly as their operations become more digitally connected.
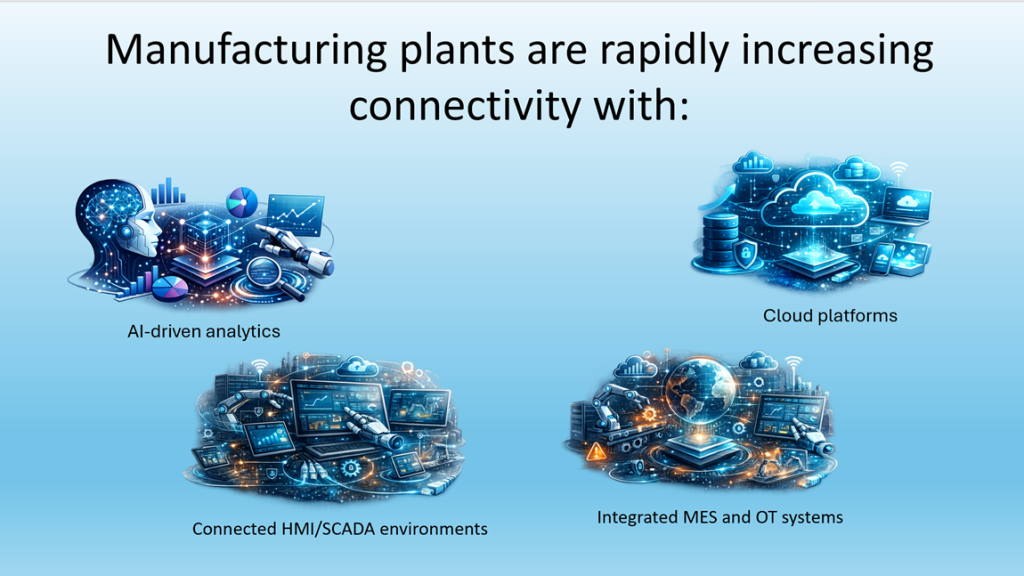
At the same time, manufacturing plants are rapidly increasing connectivity as they adopt technologies such as:
– AI-driven analytics
– Cloud platforms
– Integrated MES and OT systems
– Connected HMI/SCADA environments
These technologies provide clear benefits by improving operational efficiency, visibility, and decision-making. However, they also expand the potential attack surface inside the plant.
Every new connection between a machine, an HMI/SCADA system, an analytics platform, or an enterprise application represents another potential entry point for cyber threats.
The implication is clear: as manufacturers pursue AI-enabled initiatives and smarter digital operations, connectivity increases, and with it comes greater exposure.
Industrial cybersecurity can no longer be treated as an afterthought. It must be designed into the architecture of modern automation systems from the start, ensuring that operational innovation does not introduce unacceptable risk.

What Can We Learn from 2025?
It is difficult to say that any organization can completely avoid a cybersecurity incident. However, there are practical steps manufacturers can take to reduce their risk and strengthen their operational resilience significantly.
Some of the most important lessons from 2025 include the following cybersecurity practices that manufacturers, especially small-to-mid-market organizations, should implement to strengthen their defenses:
– Improve visibility and network segmentation.
Manufacturers must maintain clear visibility into their OT environments and segment critical systems so that a breach in one area does not spread across the entire operation. The Purdue Model remains a useful framework for industrial environments because it emphasizes segmentation, defense-in-depth, and risk management across multiple layers of the control architecture (see the blog by Fortinet). The use of firewalls on external endpoints and between segments is critical for preventing unauthorized access and extracting data from the manufacturing plant.
– Identify and manage connected assets.
Organizations should maintain an accurate inventory of all connected equipment, including PLCs, HMIs, servers, engineering workstations, and network devices. Mapping these assets helps organizations understand what is connected to the network and identify potential vulnerabilities. Unused network ports, services, and interfaces should be disabled to reduce the overall attack surface.
– Implement secure remote access.
Remote connectivity is often necessary for system integrators, vendors, and maintenance teams, but it must be tightly controlled. Organizations should use dedicated secure remote access solutions that support strong authentication, session logging, monitoring, and granular, time-limited access for external users.
– Inspect inbound files and connected devices.
Files, USB drives, laptops, and external devices entering the plant environment should be scanned and verified before being allowed to connect to operational systems.
– Secure wireless networks.
Wi-Fi networks should be encrypted, hidden when possible, and protected with strong passwords and proper network access controls to prevent unauthorized access to plant systems.
– Enable multi-factor authentication (MFA).
Multi-factor authentication significantly reduces the risk of unauthorized access by requiring an additional verification step, such as a one-time passcode, hardware security key, or biometric login.
– Maintain strong password hygiene.
Organizations should enforce strong password policies, avoid password reuse across accounts, and monitor for compromised credentials. Password management tools and dark web monitoring services can help identify exposed credentials before they are exploited.
– Implement a 3-2-1 backup strategy.
Maintain three copies of critical data, stored on two different media types, with at least one copy kept offline or offsite. Regular, automated backups ensure that operations can be restored in the event of ransomware or other disruptive attacks.
– Train employees regularly.
Conduct ongoing cybersecurity training and simulation exercises to help employees recognize phishing attempts, social engineering attacks, and emerging threats, including AI-generated phishing emails and deepfakes.
For additional guidance, the Cybersecurity & Infrastructure Security Agency (CISA) provides practical cybersecurity resources and recommendations specifically designed to help small businesses strengthen their security posture.
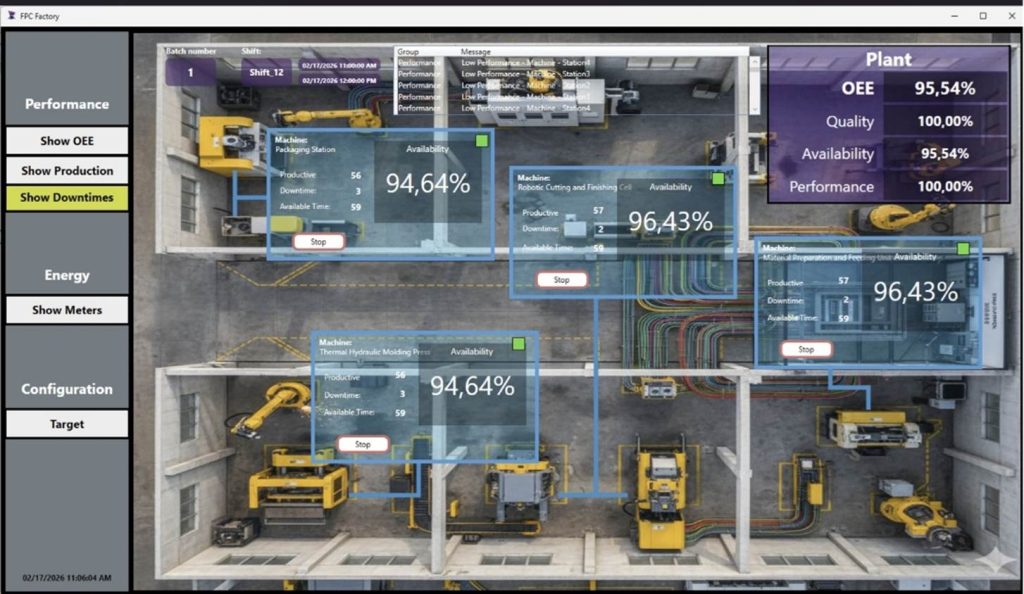
Securing SCADA and HMI Systems: A Holistic Approach
SCADA (Supervisory Control and Data Acquisition) and HMI (Human-Machine Interface) systems play a critical role in the daily operations of many small- to mid-market manufacturing plants. These systems provide visibility into processes, enable operators to interact with equipment, and help maintain stable, efficient production.
As the cybersecurity lessons from 2025 demonstrate, industrial environments are becoming increasingly attractive targets for cyberattacks. Because HMI and SCADA platforms sit at the center of plant operations, they must be designed and deployed within a secure automation architecture.
However, protecting these systems cannot rely solely on the security features of a single software platform. Effective protection requires a holistic approach across the entire operational technology (OT) environment, including network segmentation, secure remote access, asset visibility, strong authentication, disciplined operational practices, and employee awareness.
For manufacturers, cybersecurity must be designed into the architecture of modern automation systems from the beginning, ensuring that increased connectivity, AI-driven analytics, and digital transformation initiatives do not introduce unacceptable operational risk.
At ADISRA, cybersecurity is a key design consideration in our software platforms, helping manufacturers deploy secure and scalable industrial visualization and analytics solutions.
Try ADISRA SmartView: Download a free trial of our HMI/SCADA software on our website here.
Explore InsightView and KnowledgeView: Request a temporary account at info@adisra.com to experience our OEE analytics and predictive maintenance platforms.
Visit our website at: www.adisra.com
If you are interested in learning more about ADISRA SmartView, we invite you to attend our upcoming webinar. Additional details are provided below.

ADISRA SmartView on Linux: Flexible HMI/SCADA for Modern Industrial Systems
In a world increasingly shaped by proprietary ecosystems and large technology platforms, Linux continues to quietly grow as a powerful alternative. While Windows still dominates the desktop market with approximately 73.72% global market share, Linux is rapidly expanding across industrial systems and edge computing.
According to Research and Markets, the Linux operating system market is expected to reach $18.73 billion by 2029. In industrial automation, adoption is already accelerating. SQ Magazine reports that Linux-based PLCs represent 33.1% of newly deployed systems, and 71.9% of edge AI inference workloads run on Linux.
These trends make one thing clear: Linux is becoming a critical platform for modern industrial automation.
Join us for this upcoming webinar where we will demonstrate how to build scalable and robust HMI/SCADA applications using ADISRA SmartView on Linux.
During the session, we will cover:
– Design considerations for Linux deployments.
– Connectivity & Integration – bridging PLCs and databases.
– Security & Maintenance best practices for Linux environments
– Remote Management of your ADISRa SmartView application.
– Edge AI Integration – running an AI expert system using built in rule-based system for predictive maintenance
If Linux is part of your automation strategy, or will be soon, this webinar will show you how ADISRA SmartView enables industrial applications on the Linux platform.
Join us on March 26th, at
7:30 am PDT
9:30 am CDT
3:30 pm CET
4:30 pm EET
9:30 pm WIB
10:30 pm – SGT
Register for the webinar here.
We look forward to seeing you there.
ADISRA®, ADISRA’S logo, InsightView®, and KnowledgeView® are registered trademarks of
© 2026 ADISRA, LLC. All Rights Reserved.
